Over the past decade, digital assets have quietly moved from experimental technology into something much more serious: financial infrastructure. Banks, asset managers, fintech companies, and sovereign investors are all studying how blockchain systems might fit into the architecture of modern finance. Yet in almost every institutional conversation about crypto, one question still surfaces early—sometimes politely, sometimes bluntly: Can this infrastructure actually be trusted at scale?
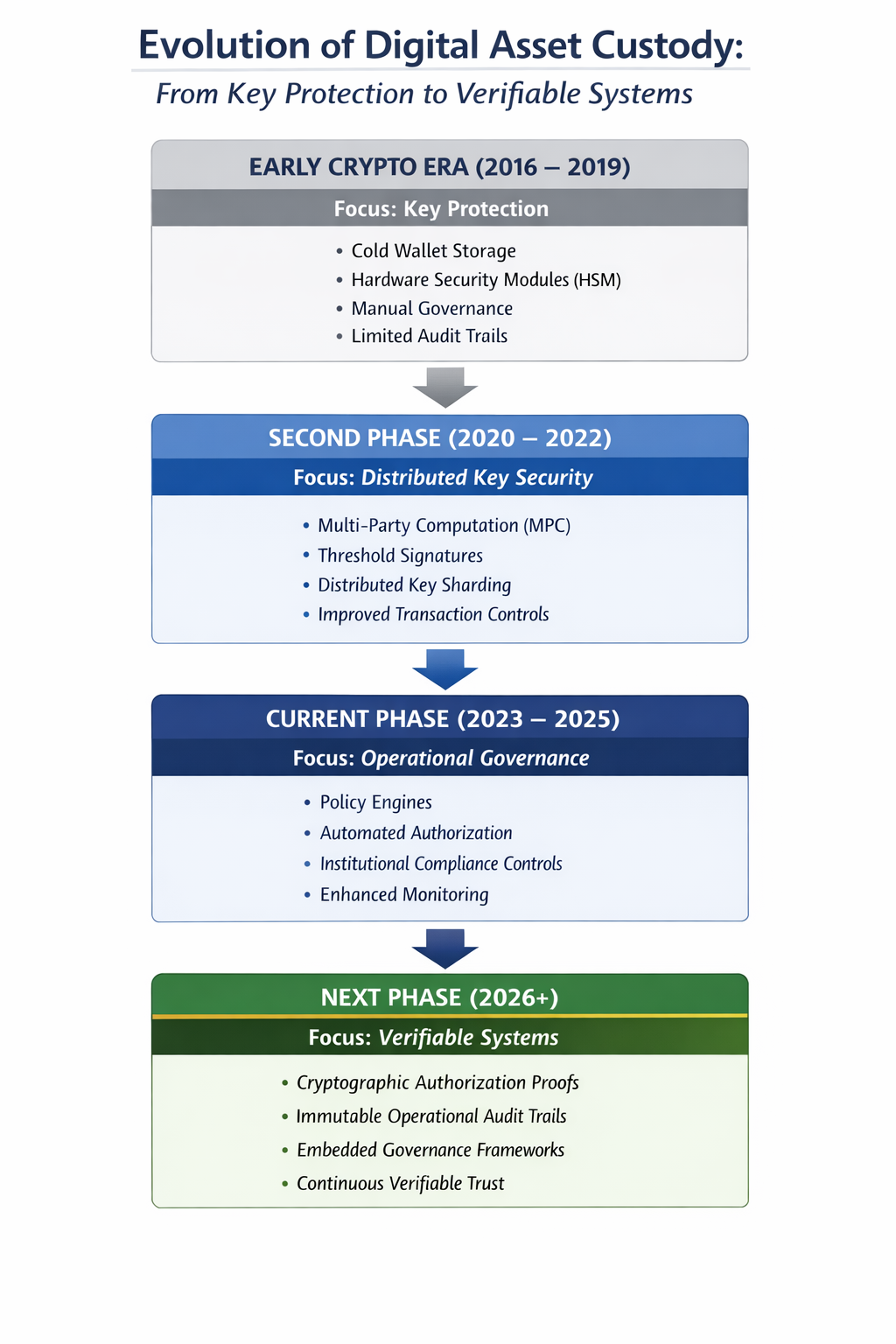
For years the industry answered that question with a fairly simple premise. Secure the private key and the asset remains secure. In principle that logic still holds. Modern cryptography is exceptionally resilient, and the ecosystem has invested heavily in technologies designed to protect keys—MPC wallets, hardware security modules, distributed signing protocols, and hardened wallet architectures. These advances transformed what used to be fragile operational setups into something much closer to digital asset custody infrastructure.
Anyone who worked in the early years of the ecosystem remembers how improvised things sometimes looked. Seed phrases scribbled on paper. Approval workflows dependent on a handful of trusted individuals. Operational visibility that felt closer to a startup dashboard than a financial control system. Compared with that environment, the current generation of secure wallet infrastructure is dramatically more mature.
And yet, as institutional participation grows, the industry is learning something important. Protecting keys is necessary—but it isn’t the whole story anymore.
In practice, the cryptographic layer rarely fails. Encryption algorithms tend to perform exactly as designed. Where complexity begins to creep in is the operational layer around the key: the authorization logic, governance framework, policy enforcement, and the system’s ability to prove what actually happened after a transaction is executed. These components may sound less glamorous than cryptography, but they are exactly what institutional investors evaluate when assessing institutional crypto custody solutions.
When security reviews take place, the questions rarely revolve around elliptic curves or signature schemes. They tend to be much simpler—and sometimes more revealing. Who approved the transaction? Under which policy? And can the system still prove that approval months later?
That last point matters more than many engineers initially expect. In traditional finance, the ability to demonstrate accountability is just as important as preventing unauthorized access. Auditability is not an afterthought; it is part of the infrastructure itself. Yet if we’re being honest, some early digital-asset systems treated audit trails as secondary features rather than foundational components.
Here is a hard truth that regulators frequently raise in private conversations: a surprising number of early “audit logs” across crypto platforms were little more than exported files or system records. In other words, what was meant to serve as operational evidence sometimes ended up looking like a spreadsheet extract. That may have been acceptable during the experimental phase of crypto infrastructure. It will not be acceptable as the industry scales into institutional finance.
According to several blockchain analytics reports, more than $20 billion in digital assets has been lost across exchanges, bridges, and custodial systems over the past decade. Very rarely did those incidents involve broken cryptography. Instead, they exposed weaknesses in governance, operational oversight, or transaction authorization. The lesson is becoming increasingly clear: security failures are rarely mathematical—they are systemic.
Why Cryptography Is No Longer the Bottleneck
For most of the last decade, the conversation around digital-asset security focused almost entirely on private-key protection. Technologies such as MPC wallets and threshold signature schemes emerged precisely to address that challenge, distributing trust across multiple participants so that no single entity controls the full signing authority. These innovations remain essential, and they continue to underpin modern enterprise crypto custody platforms.
But the threat model has evolved. Today, security discussions increasingly revolve around governance, policy enforcement, and operational transparency. In other words, the question has shifted from “Is the key safe?” to something broader: “Is the entire system behaving as expected?”
We’re finally seeing authorization evolve from “someone clicked approve” to “the system generated cryptographic proof that the approval happened.” That difference might sound subtle, but from an infrastructure standpoint it represents a significant shift. Systems are beginning to produce verifiable evidence for every step in a transaction lifecycle.
From Secure Systems to Verifiable Systems
The next phase of innovation in digital asset custody architecture focuses less on inventing new cryptographic primitives and more on connecting security components into verifiable systems. The idea is straightforward: ensure that authorization, governance policy, and auditability are cryptographically linked so that every transaction decision can be independently validated.
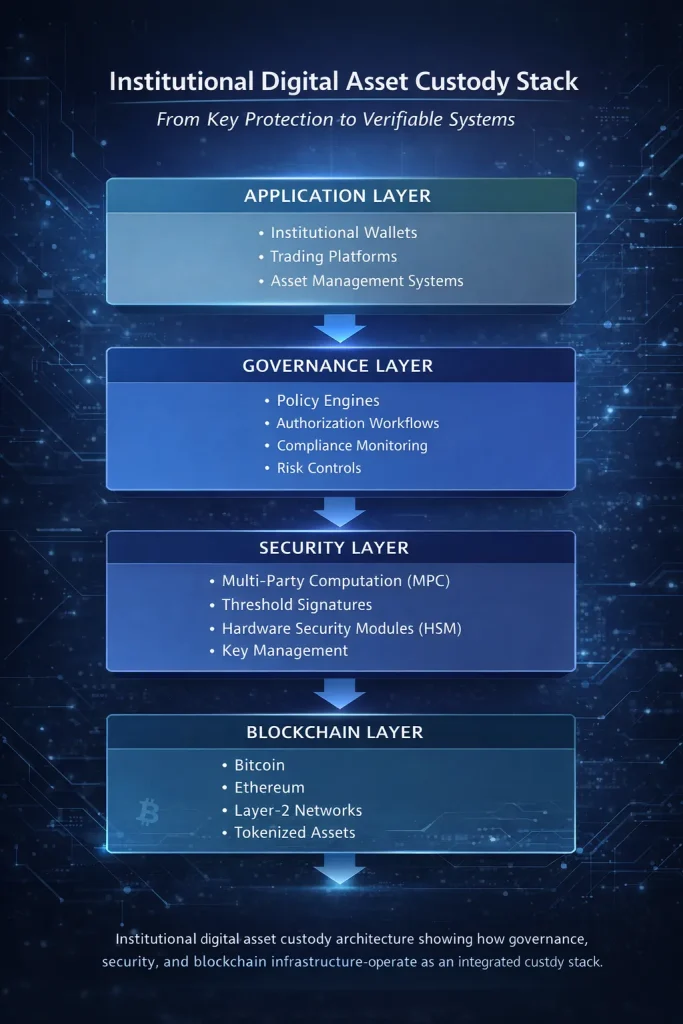
In practical terms, several architectural shifts are already underway:
- Cryptographically attested authorization: Approvals are tied to verifiable identities and policy conditions, ensuring that authorization events cannot be disputed later.
- Immutable operational audit trails: Transaction decisions generate tamper-evident records rather than editable logs, improving forensic transparency.
- Embedded governance frameworks: Policy enforcement moves closer to the system architecture itself, reducing the reliance on manual controls or external interpretation.
These developments are gradually reshaping how institutional digital asset custody infrastructure is designed and evaluated. Interestingly, some of the most sophisticated experimentation is happening in regions where digital-asset adoption intersects with strong regulatory expectations. Markets across Asia and the Middle East, for example, increasingly expect infrastructure providers to demonstrate not only security but verifiable operational integrity.
In those environments, security cannot remain a black box. Systems must prove their integrity continuously.
Where Institutional Trust Actually Comes From
At organizations like Liminal Custody, the goal has never been simply to add more layers of protection around digital assets. The deeper challenge is closing a structural gap that existed in many early platforms: the absence of provable orchestration between identity, policy, and transaction execution.
Security rarely fails because encryption breaks. Instead, failures tend to appear at the seams between systems—the point where identity verification hands off to authorization logic, or where governance rules are interpreted by application code. When those seams are eliminated, something powerful happens. Authorization, policy enforcement, and auditability become part of a single cryptographic framework.
That integration changes how institutions evaluate risk. Instead of relying on operational assurances, they can examine systems that demonstrate trust mathematically. And for institutions responsible for safeguarding billions in capital, that difference is significant.
A More Mature Phase for Digital Asset Infrastructure
Every major financial technology follows a similar path. Early experimentation exposes weaknesses. Engineers refine architecture. Regulators establish clearer expectations. Eventually, the infrastructure matures.
Digital assets are now entering that phase.
Five years ago, many institutions were still asking whether blockchain systems could safely secure large pools of capital. Today the conversation has evolved. The real question is no longer simply “are the keys secure?” Instead it is “can the entire custody system prove that it behaved correctly?”
That shift is not a warning sign—it is evidence of progress. When markets begin demanding provable governance, verifiable authorization, and immutable operational evidence, infrastructure inevitably improves.
And that improvement is already visible. The digital asset ecosystem is moving toward a future where trust is not assumed but demonstrated—where every approval can be verified, every governance rule enforced transparently, and every transaction supported by cryptographic evidence.
The past decade taught the industry how to protect digital assets. The decade ahead will focus on proving the systems that govern them. When that transition is complete, digital asset custody will stop looking experimental and start looking exactly like what institutions expect: reliable financial infrastructure.
Read More

$100 Billion Later
Five years ago, I started
Liminal because of a simple
but frustrating observation…

The Infrastructure Moment
Five years into building Liminal Custody, what stands out is not just the pace of growth in…

The Verifiable Future
Digital asset security is not collapsing under visible pressure. Instead, it is deteriorating…
