
The Illusion of Progress
Digital asset security is not collapsing under visible pressure. Instead, it is deteriorating quietly beneath layers of perceived sophistication.
Over the last five years, the industry has adopted increasingly advanced infrastructure—MPC wallets, distributed key architectures, multi-party authorization systems, and automated custody frameworks. On paper, these developments signal maturity and progress in the way digital assets are secured and managed. Yet reality tells a different story.
Despite the spread of sophisticated custody tooling, crypto thefts and infrastructure compromises continue to scale into the billions annually, according to the Chainalysis Crypto Crime Report.
The issue, however, is rarely cryptography itself. Modern cryptographic primitives remain extremely resilient. The real problem lies elsewhere—in how trust is operationalized inside the systems that use them.
Too often, institutions assume that distribution automatically implies security. In practice, distribution without verifiability often introduces new layers of opacity. And opacity is where risk hides.
The Custody Paradox: Distribution Without Verifiability
Modern digital asset custody architectures rely heavily on multi-party computation (MPC) and distributed authorization models. These systems fragment private key ownership across multiple parties or environments, eliminating traditional single points of failure and reducing the likelihood of unilateral control.
This design is necessary. But it is not sufficient.
While MPC protects key material, it does not automatically guarantee the integrity of the broader operational environment surrounding it. In real-world deployments, weaknesses often emerge around the cryptography rather than inside it.
Three structural risks appear repeatedly across institutional custody systems.
The first is coordination risk. Distributed keys frequently depend on centralized orchestration layers to coordinate signing workflows. If those orchestration layers are compromised or misconfigured, the distributed architecture itself may provide little protection.
The second is collusion risk. Threshold cryptographic systems assume independence between participants involved in signing or authorization processes. In operational environments, however, that independence may not always hold under pressure or internal compromise.
The third is recovery injection risk. Emergency recovery workflows, designed to restore access during failures or operational crises, often bypass the original trust assumptions protecting the system in normal operation.
These risks rarely appear in architecture diagrams.
Yet they represent some of the most consequential failure modes in institutional digital asset custody infrastructure.
The Verifiability Gap
Institutional confidence in custody infrastructure still relies heavily on familiar mechanisms: security audits, process documentation, and access reviews. These controls remain necessary, but in high-value digital asset environments they are no longer sufficient.
Traditional security verification relies largely on retrospective observation. Logs are reviewed. Processes are validated. Access permissions are checked.
But this model has limitations.
- Logs can be altered.
- Processes can be bypassed.
- Controls can be misconfigured.
In effect, the system is trusted only after the fact. That model does not scale for digital asset systems operating globally and managing billions in value.
Security must therefore evolve from observable to provable.
A custody system should not be trusted simply because it has been audited. It should be trusted because its behavior can be independently verified in real time.
The emerging operational standard for digital asset custody therefore rests on three principles: transactions should carry verifiable cryptographic proofs, authorization should be enforced mathematically rather than operationally, and execution trails should be tamper-evident by design.
This shift moves security closer to deterministic systems engineering rather than procedural oversight.
The CISO Maturity Model Is Changing
As digital asset infrastructure matures, the metrics by which CISOs evaluate custody platforms are evolving.
Historically, security programs emphasized perimeter defense—protecting keys, systems, and networks from external intrusion. The next generation of security architecture, however, will emphasize structural integrity and provability.
Three emerging indicators are beginning to define this shift.
The first is authorization velocity versus proof ratio. In earlier security models, organizations often equated safety with friction. The more manual approvals a transaction required, the more secure the system appeared.
But friction does not equal security.
The next generation of custody infrastructure will focus instead on cryptographic authorization velocity: the ability to execute transactions rapidly while embedding verifiable proof directly into the authorization process itself.
The goal is not slower systems. The goal is systems in which unauthorized transactions become mathematically impossible.
Rather than relying on human confirmation that something was approved, infrastructure itself should enforce the rule that transactions cannot move without cryptographic consensus.
The second indicator is recovery independence. Recovery mechanisms remain one of the least discussed—yet most dangerous—components of custody architecture.
If a recovery environment depends on the same hardware, personnel, or cloud infrastructure as the primary signing system, it does not represent resilience. It simply mirrors the original failure domain.
Robust custody architectures require recovery independence: recovery frameworks that operate with minimal shared dependencies and function as parallel trust systems that are continuously tested and independently verifiable.
Many breaches historically attributed to key compromise begin with weaknesses in recovery workflows. Security failures rarely start where people expect them.
The third indicator is jurisdictional fluidity. Regulatory fragmentation is rapidly becoming one of the defining operational challenges for global digital asset institutions.
Custody systems increasingly operate across jurisdictions that demand different reporting standards, compliance signals, and verification models. A one-size-fits-all infrastructure approach therefore becomes a liability.
Future-ready custody environments must support jurisdiction-aware verification, where infrastructure dynamically attaches compliance proofs based on the geographic and regulatory context of each transaction.
Regulatory bodies such as the Bank for International Settlements have increasingly emphasized the importance of provable custody controls in cross-border digital asset systems. Infrastructure that cannot adapt to these requirements will struggle to scale globally.
From Key Management to Trust Management
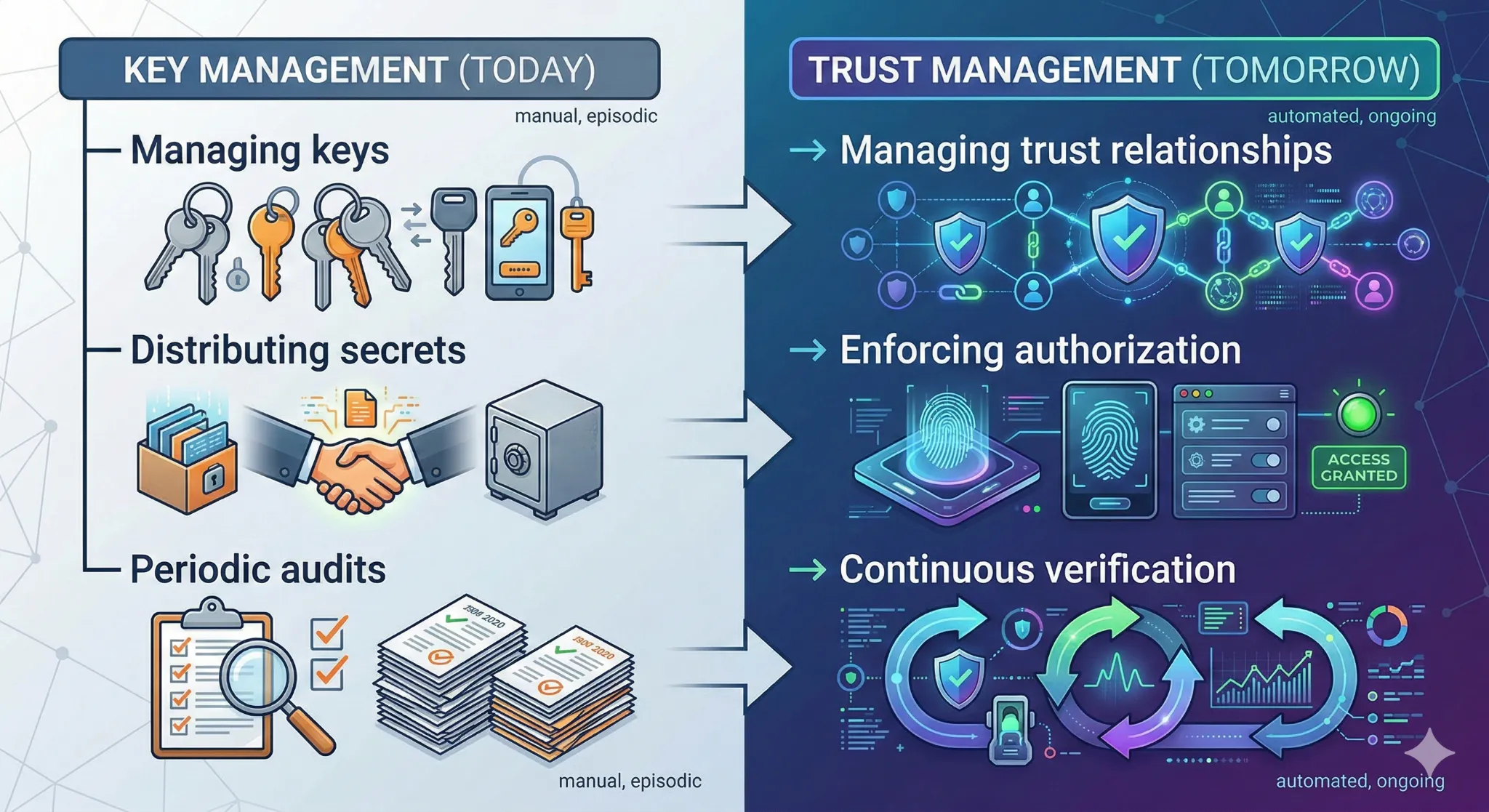
For much of the last decade, digital asset security discussions focused primarily on key management—how keys are generated, stored, and protected.
However, institutional adoption is shifting the conversation toward something broader: trust management.
Key management protects secrets. Trust management governs relationships between systems, institutions, and participants.
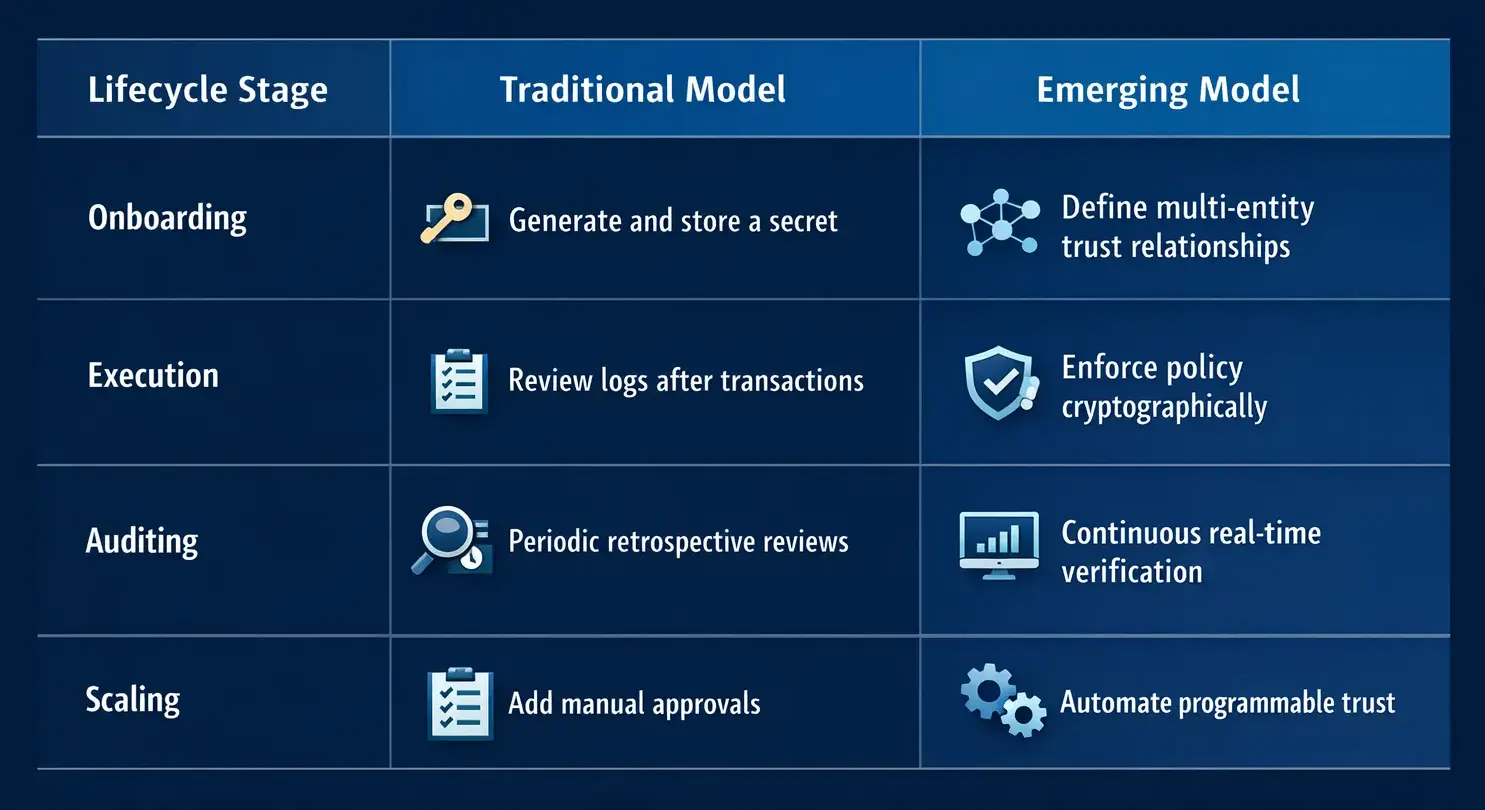
In this emerging model, security becomes less dependent on procedural discipline and more dependent on cryptographic guarantees embedded directly into system behavior.
The Era of the Zero-Assumption CISO
The most effective security leaders increasingly share one defining trait: they assume that processes eventually fail.
Humans become tired. Operational environments drift. Procedures degrade over time.
Cryptographic systems, however, operate under deterministic constraints.
The next phase of digital asset security will therefore center on minimizing reliance on human assumptions and maximizing mathematically enforceable controls.
For CISOs responsible for institutional custody platforms, the key question is no longer simply: Is this system secure?
The more relevant question is: Can this system prove its security continuously and independently?
Because the future of financial infrastructure will not be defined by systems that merely ask for trust. It will be defined by systems that demonstrate trust—every single time they operate. And in security architecture, mathematics rarely gets tiring.
Read More
The Next Era of Digital Asset
Over the past decade, digital assets have quietly moved from experimental technology…

Building Trust at Scale
Digital asset infrastructure is entering a phase of operational maturity. Institutional…

Five Years of Building Trust
When I relocated to Dubai around eighteen months ago, I entered a financial ecosystem that was…
